What is 2FA?
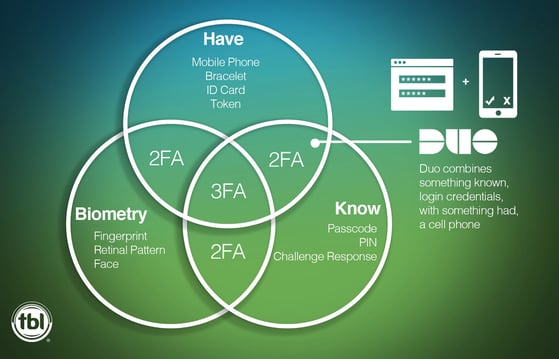
2FA stands for “Two factor authentication.”
2FA strengthens access security by requiring two authentication factors, or credentials, to verify user identities.
These factors can include combining:
- Something you know
- Such as: a passcode, a PIN
- Something you have
- Such as: a smart phone, a token
What does 2FA Protect Against?
2FA protects against phishing, social engineering and password brute-force attacks and secures your logins from attackers exploiting weak or stolen credentials.
What is DUO and How Does it Work?
Duo is a security tool offering 2-factor authentication via a mobile phone application. Working with the input of a username and password, a second authentication method is leveraged. For that second authentication method, Duo utilizes one of either:
- Push Notification
- Phone Call
- Text Message
Upon setting up Duo, the admin can choose what the second form of authentication is.
How does Duo Support Zero Trust?
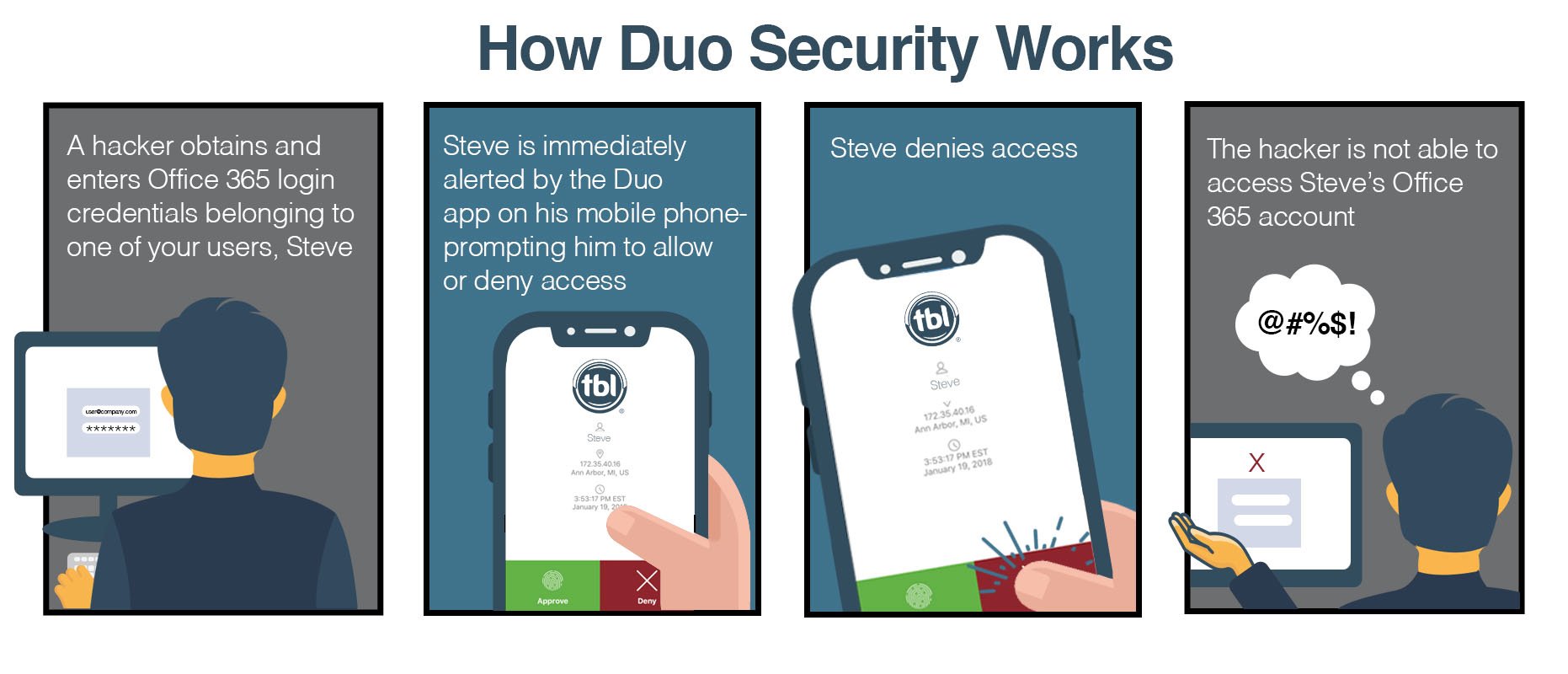
Zero Trust defense is built on the fundamental rule of don’t trust anyone.
Duo upholds Zero Trust by assuming any log in attempt is the result of compromised credentials. In order for access to be granted via log in, the user must verify their identity- proving they are who they claim to be. That verification comes from Duo’s mobile application.
What Makes Duo simple for Users?
The less strain security measures put on users, the more likely users are to comply. Duo was designed for ease of use and because of this, Duo has been successful in delivering a solution that doesn’t significantly impede user workflow.
Duo has become well known for:
- It’s ability to be easily to accessed
- Low cost
- Allowing users to react quickly
- Not overburdening users with security measures
- It’s push method ease of use
You can Try Duo for Free
Sign up for a free 30-day trial (below) to start securing your users in minutes.
That includes everything in Duo MFA:
- Protect logins with two-factor authentication and easily enroll and manage users
- Automate the management of your Duo solution (i.e. admin APIs)
- Get an overview of device security hygiene
- Protect on-premises apps and federated cloud apps
- Single sign-on (SSO) for cloud applications